The NY Times says nobody knows how the FBI decrypted the infamous iPhone. That is certainly true, but there is speculation about physically opening up one of its chips and reading its crypto key. http://www.nytimes.com/aponline/2016/03/29/us/politics/ap-us-apple-encryption.html Years ago, I looked at reverse engineering of chip designs by physically disassembling them. Here are some comments on how difficult this is, although it certainly may be possible.
Physically attacking a chip is an old, but difficult, method of breaking into a system that you control. In 2008, Ed Felton and others read DRAM chips that had been turned off, by freezing them in liquid nitrogen. But they were reading the outside pins of the chip package. http://www.nytimes.com/2008/02/22/technology/22chip.html Partly to prevent that, but mostly for speed and cost reasons, processors like those inside a smart phone now include modules like graphics, cache, and security on the same die and chip. So there is no way to read such data from outside the package, unless a design has a bug.
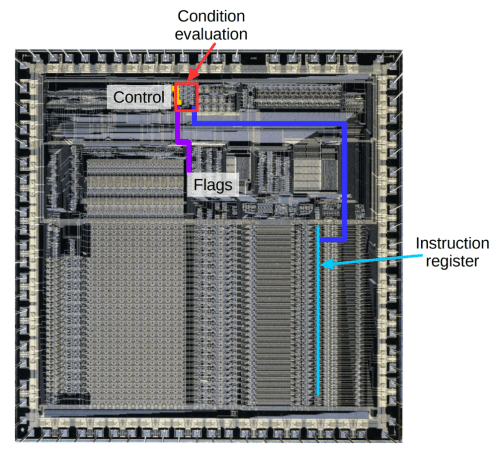
To read signals from inside a chip, you need to figure out the logical and physical layouts of the chip, which are proprietary and, with up to 100 million logic gates, very complex. Then you need to be able to inject and read signals with a physical separation of 100 nanometers(nm) or less. By comparison, the wavelength of light is 400 nm or greater. And the chip designers knew you might try, and perhaps did their best to make it impossible. Of course, companies still attempt to reverse engineer their competitors’ chips, so some expertise does exist.
Finally, if you are physically slicing up a unique device, I would guess that one slip and you may not be able to recover. You can’t just shut off power and start over the way you can with software attacks.
Here is one example of successfully dissecting a security chip, back in 2010. It was not easy!